SPEARHEAD
Intelligence. Weaponized.
A multi-agent system that simulates the full spear phishing lifecycle — from OSINT to personalized attack — for defensive security research.
“The best way to defend against a sophisticated attack is to understand how one is built.”
SpearHead is a university research project (TFG) that automates the full spear phishing lifecycle using large language models and a Neo4j knowledge graph. It was built for Red Team engagements, Blue Team defense training, and academic institutions who need to understand realistic attack vectors in a controlled, authorized environment.
The system chains five specialized agents — OSINT gathering, entity profiling, attack synthesis, quality review, and defense testing via SpearDetector — enabling Red Teams to simulate targeted campaigns and Blue Teams to validate their detection capabilities, all from a single command.
Built for Red Teams.
Essential for Blue Teams.
Simulate real attack campaigns for Red Team audits, or use the full pipeline to understand adversary techniques and harden your defenses.
Autonomous OSINT
Scout Agent runs 9 sequential passes: DuckDuckGo, GitHub, Wayback Machine, Hunter.io, WHOIS, DNS, crt.sh, HIBP breach check, and Apify social media (Instagram, TikTok, Twitter/X). Batch up to 10 targets per run. Deep search mode doubles coverage.
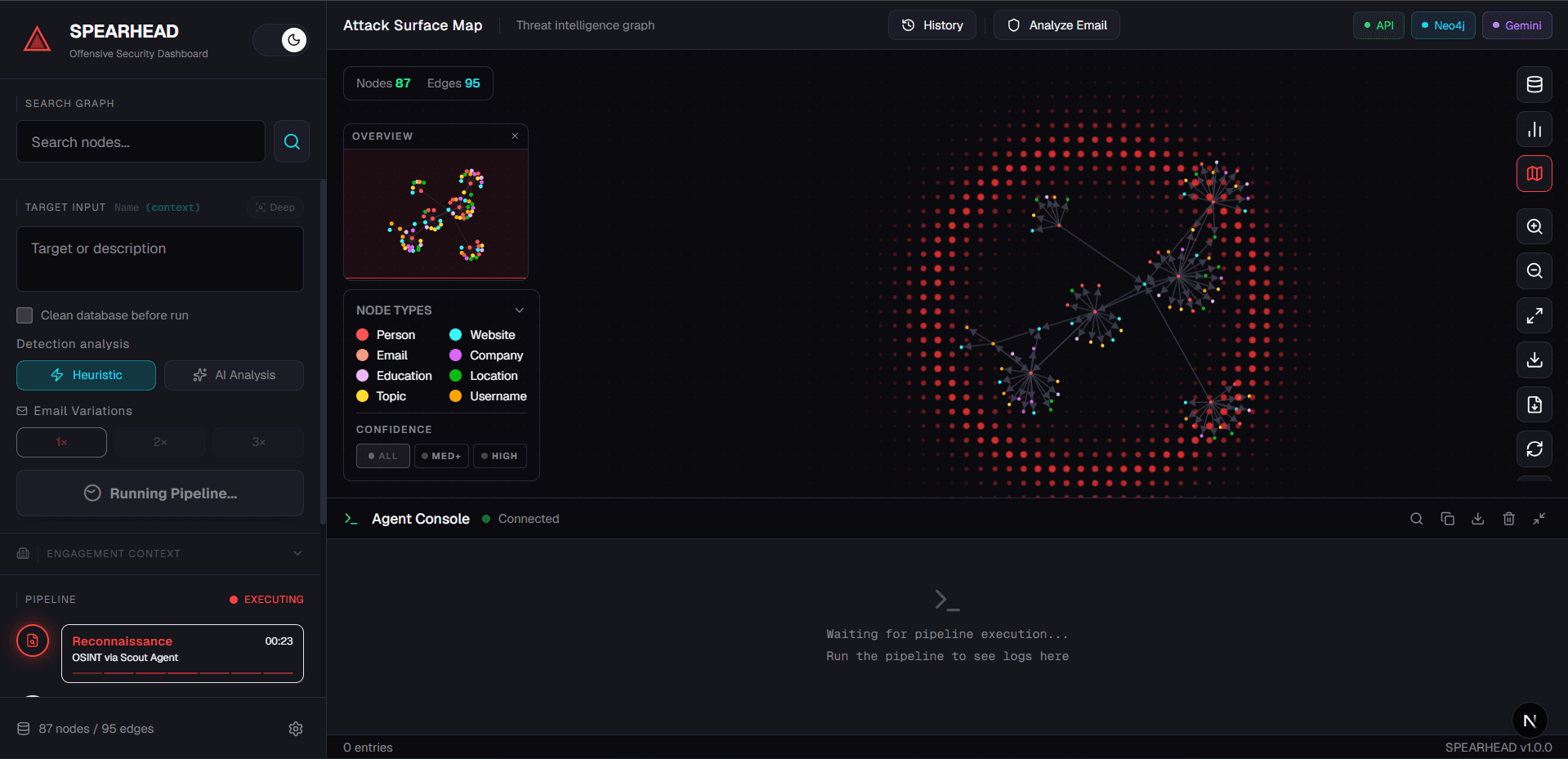
Annotated Knowledge Graph
Profiler Agent builds a Neo4j graph with full source evidence per node. Annotate nodes as Confirmed / False Positive / Needs Review. Export as CSV or GEXF for Gephi.
AI Attack Synthesis
Attack Agent uses RAG over the knowledge graph to generate 1–3 variations per target across distinct persuasion angles: Authority, Rapport, and Opportunity. Compare them side-by-side in the dashboard, or right-click any node to generate instantly.
Quality Scoring & Defense
Reviewer Agent scores every draft 0–10 on persuasiveness, deliverability, and detection resistance — with a structured critique and improved version. SpearDetector then independently validates each output using entropy analysis, multilingual keyword detection, and link inspection, closing the offense–defense loop.
Built-in Detector
SpearDetector analyzes emails with entropy scoring, multilingual keyword detection, suspicious link inspection, and optional AI mode — consistently rating SpearHead-generated content HIGH RISK and validating both sides of the loop.
Operational Dashboard
WebSocket-powered Next.js dashboard: live searchable log terminal, interactive force-directed graph, engagement context (org scope), batch progress tracking, resumable runs via checkpoints, fullscreen graph mode, and searchable run history.
Intelligence visualized in real time.
Monitor every agent, inspect the knowledge graph, and review generated attacks — all from a single WebSocket-powered interface.
From one name to a complete intelligence map
The Profiler Agent maps every discovered entity — social profiles, companies, locations, topics, and domains — into a live Neo4j knowledge graph. The Attack Agent traverses this graph to craft hyper-personalized phishing content.
↻ interactive · drag to rotate · click nodes to highlight
One Tool. Three Missions.
Whether you're running a Red Team engagement, training defenders, or writing your thesis — SpearHead adapts to your mission.
Red Team Engagement
Automate the full spear phishing kill chain — from target OSINT to a tailored email ready for delivery.
Blue Team Training
Run realistic phishing simulations against your own team and measure how well SpearDetector catches them.
Academic Research
Study LLM-based social engineering pipelines and produce structured reports for academic documentation.
Five Agents. One Objective.
Each agent specializes in one phase. Together they form an autonomous, end-to-end spear phishing simulation pipeline.
Scout
OSINT crawl
Profiler
Knowledge graph
Attack
Email synthesis
Reviewer
Quality scoring
Detector
Defense test
Reporting
HTML & PDF report
PROScout Agent
OSINT crawl
Profiler Agent
Knowledge graph
Attack Agent
Email synthesis
Reviewer Agent
Quality scoring
Detector Agent
Defense test
Reporting Agent
HTML & PDF report
PRO TIERPowered by
Choose Your Path
SpearHead is fully open source. Use it for Red Team audits, phishing simulations, or academic research. The Pro tier unlocks structured reporting.
- Scout Agent — 9 OSINT passes incl. HIBP & Apify
- Profiler Agent (Neo4j Knowledge Graph)
- Attack Agent — up to 3 variations per target
- Reviewer Agent (Quality Scoring 0–10)
- SpearDetector (Heuristic + AI mode)
- Real-time Next.js Dashboard
- Batch processing — up to 10 targets per run
- Resumable pipeline runs (checkpoint system)
- Multi-provider LLM (Ollama, Gemini, Claude, OpenAI)
- WebSocket live log streaming with search
- Graph export (CSV + GEXF for Gephi)
- Report history with search
- Full source code — MIT License
- HTML Report GenerationPRO
- PDF ExportPRO
- Everything in Free
- HTML Report Generation (full styled)
- PDF Export via Chromium engine
- Priority support
- Custom LLM integration
Designed for Red Team engagements, phishing simulations, and academic research. Pro unlocks full audit reporting: styled HTML reports, one-click PDF export (Chromium-rendered), and a history panel for all previous runs. Instant delivery — install with a single pip install command.
Common Questions
Everything you need to know about SpearHead — legality, setup, pricing, and how it works under the hood.
Enterprise & Support
Need a custom deployment, volume licensing, or have a question about your Pro purchase? Fill out the form and we'll reply within 48 hours.